4 Reasons Cybersecurity Attack Surfaces Are Expanding

The COVID-19 pandemic impacted individuals and businesses worldwide, drastically altering daily routines and operational models almost overnight. Amidst the chaos, the cyber landscape experienced unprecedented changes, significantly expanding cybersecurity attack surfaces. This rapid transformation has left many businesses vulnerable, highlighting the critical need for robust cybersecurity strategies. Here are four key reasons why cybersecurity attack […]
Your Biggest Cybersecurity Risk: Your Employees

Cybercriminals don’t sleep — and they don’t need to. Automated attack tools and advanced tactics are being deployed around the clock to find and exploit weaknesses in business networks. While most companies focus on software and infrastructure defenses, they often overlook the biggest cybersecurity risk: their employees. With remote work gaining traction and decentralized workspaces […]
Vision Computer Solutions Named Top MSP Worldwide in 2021

Vision Computer Solutions is pleased to announce it has been named a premier managed service provider (MSP) worldwide by Channel Futures MSP 501 for 2021. “We are very excited to be ranked among the best MSPs in the world,” said Charles Lobert, Vice President of Sales and Marketing at Vision. “We couldn’t be successful without […]
Empower Your Employees with Windows Virtual Desktop

Enhancing Productivity and Security with Virtual Desktop Solutions Throughout the pandemic, businesses worldwide had to pivot to remote work to prioritize the safety of their employees and clients. While Virtual Desktop Infrastructure (VDI) is not a new technology, it has gained significant traction over the past year as an efficient way for businesses to securely […]
Explore the Benefits of Windows Virtual Desktop

Maximizing Productivity and Security with the Benefits of Windows Virtual Desktop In today’s digital world, supporting remote employees securely, cost-effectively, and productively is essential for businesses. Windows Virtual Desktop (WVD) offers a familiar desktop experience, accessible anywhere, unlocking the full potential of remote work. The Benefits of Windows Virtual Desktop for a Hybrid Workforce Work […]
What is Windows Virtual Desktop?
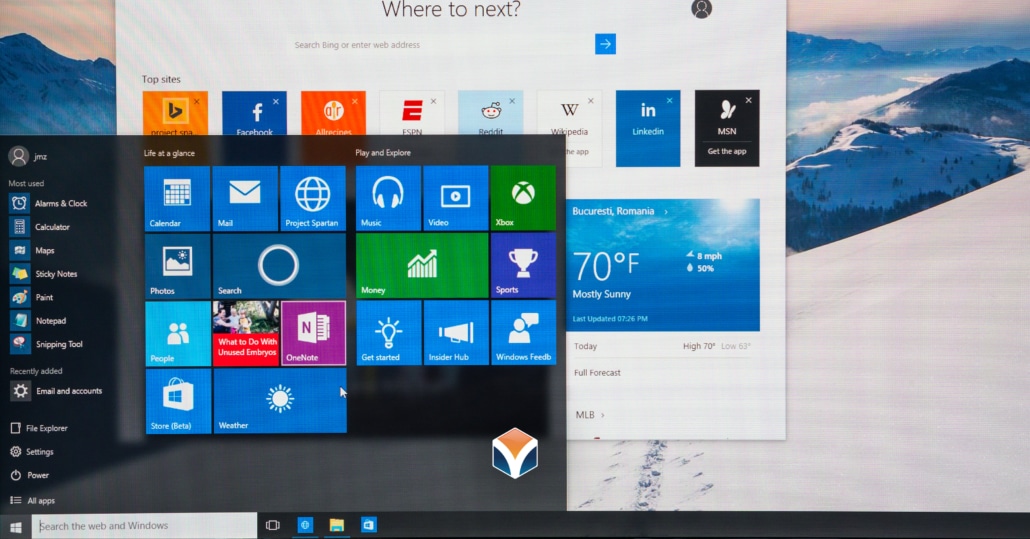
In today’s hybrid and remote-first world, businesses are looking for flexible, secure, and scalable IT solutions. Enter Windows Virtual Desktop — Microsoft’s cloud-based desktop and app virtualization service that transforms how your team works, wherever they are. What Is Windows Virtual Desktop? Windows Virtual Desktop (WVD) is a comprehensive desktop and app virtualization platform hosted […]

