What is Ransomware? (2:10)
According to Microsoft, Ransomware is a type of malware that encrypts files and folders, preventing access to important files. It attempts to extort money from victims by asking for money, usually in the form of cryptocurrencies, in exchange for the decryption key.
Did you know that ransomware cost companies over $75 billion last year? (02:30)
No company is immune to ransomware. No matter the size of your business, ransomware should still be a main concern when it comes to security. Surprisingly, the average request is about $5,000. (03:30)
What happens when your PC is attacked with ransomware? (04:08)
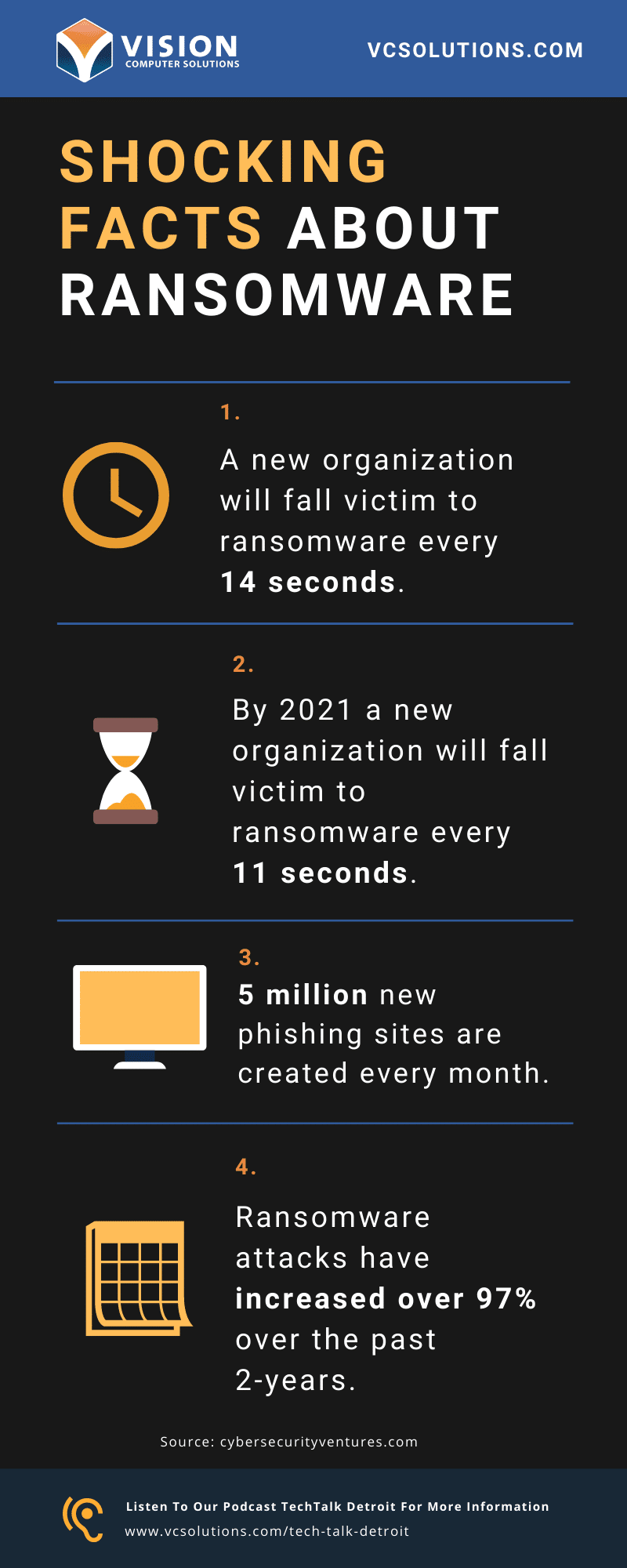
Shocking Facts About Ransomware (04:50)
- A new organization will fall victim to ransomware every 14 seconds.
- By 2021, a new organization will fall victim to ransomware every 11 seconds.
- 5 million new phishing sites are created every month.
- Ransomware attacks have increased by over 97% over the past 2 years.
- 75% of infected companies were using up-to-date anti-virus software.
50% of the companies that were surveyed for this survey did not believe their organization was properly prepared to be able to handle a ransomware attack.
Source: cybersecurityventures.com
What are the correct protections to have in place? (05:55)
- Begin with a thorough analysis of your entire network.
- Invest in firewall protection. (07:48)
- Block different countries from accessing your network. (08:05)
Some prevention best practices include:
- Secure your cloud network. (08:53)
- Backup your network. (09:51)
If all your preventative measures fail, a backup of your data is crucial for business continuity. Your backup is your #1 tool for combating ransomware.
- We partner with Datto to protect our clients’ business continuity.
Common Ransomware Infection Methods (10:36)
Phishing emails are a major way for businesses to become exposed.
- Make sure to implement email security protections such as MFA and spam protection.
- Train your users to know the difference between phishing emails and legitimate emails.
Ransomware Data Recovery (12:50)
Having the proper backup solution in place is key,
“If you have to pay for your ransom to get all of your data back,” says Chuck, “that means all of your protections have failed and you didn’t have the appropriate backup in place.”
What to do After a Ransomware Attack (15:27)
Check out some of our recent TechTalk Detroit episodes:
TechTalk Detroit EP: 23: Meet Your Hosts: Chuck Lobert & Brian Spurgeon
TechTalk Detroit EP:22: Microsoft 365 Security Best Practices
TechTalk Detroit EP: 21: 3 Ways to Reduce IT Costs

Charles Lobert, has been in the Detroit Metro Area’s IT industry for over two decades & with VCS since ’04. Throughout the years, Lobert has held nearly every position at VCS & is responsible for several major organizational shifts within VCS.